Sovereign Silicon Integrity Governance
Deterministic governance and forensic enforcement for advanced silicon systems operating at physical limits.
Deterministic black-box enforcement of silicon operating limits.
QH8 governs electrical, thermal, and mechanical stress in real time, producing auditable evidence of compliance and lifecycle margin.


Cross-domain silicon governance across power, thermal, and aging dynamics.
QH8 exposes cumulative risk that isolated design or monitoring tools cannot see.
QH8 delivers enforceable findings without modifying designs, exposing IP, or altering validation workflows.
Forensic, decision-grade outputs for engineering and executive teams.
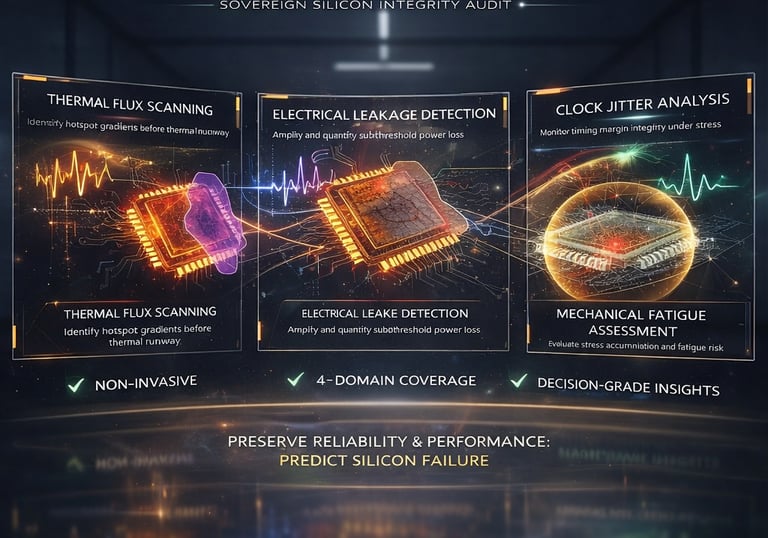



Sovereign Visibility into Silicon Integrity
Deterministic exposure of latent silicon risk under real electrical, thermal, and lifecycle stress.


System-Level Integrity Governance
QH8 governs cross-domain interactions between power delivery, thermal behavior, and cumulative aging—exposing latent failure modes in AI accelerators and advanced SoCs before field manifestation.
Sovereign Silicon Integrity Visibility
Deterministic exposure of latent silicon risk under real-world operating envelopes.
QH8 governs system-level reliability without requiring source code access, design disclosure, or hardware modification.
System-Level Semiconductor Reliability Governance
QH8 Technologies provides deterministic, system-level reliability governance for advanced silicon operating under real electrical, thermal, and mechanical stress.
QH8 enforces cross-domain integrity across power, thermal, and lifecycle dynamics—exposing latent risk that conventional simulation, monitoring, and point tools cannot govern.
1. Observe Real Behavior
Enforce Real Operating Conditions
QH8 governs silicon platforms under real electrical, thermal, and workload stress—capturing behaviors that simulations and isolated lab tests cannot enforce.
2. Govern Cross-Domain Interaction
QH8 enforces cross-domain integrity across power delivery, thermal dynamics, aging effects, and workload history—exposing cumulative risk that isolated tools cannot govern.
3. Issue Decision-Grade Forensic Outcome
QH8 issues decision-grade forensic outcomes that support engineering and executive action—without requiring source code access, hardware modification, or changes to existing validation workflows.


Infrastructure Failures Begin in Physics, Not Software
QH8 Technologies provides deterministic Infrastructure Integrity Analysis — detecting power, thermal, and transient anomalies that standard monitoring systems cannot resolve.
Zero-touch forensic analysis using your existing telemetry.
What QH8 Does
Modern infrastructure is monitored at the software layer.
Yet hardware fatigue, instability, and unexplained failures originate in:
• Power transients
• Thermal gradients
• Slew-rate anomalies
• Variance patterns invisible to sampled dashboards
QH8 operates at Layer-0 — the physical behavior layer of infrastructure.
We analyze high-resolution telemetry to reveal hidden instability, inefficiency, and unsafe dynamics before they propagate into performance degradation, hardware stress, or operational incidents.
Core Service: Infrastructure Integrity Audit
Infrastructure Integrity Audit
:
QH8 performs a zero-touch forensic analysis of your system’s physical and operational dynamics using telemetry you already collect (IPMI, BMC, NVIDIA-SMI, PDU, BMS, etc.).
No agents.
No software installation.
No production risk.
Deliverables
What You Receive
✔ Physics Anomaly Map
Visualization of power slew rates (dP/dt), thermal gradients (dT/dt), and variance patterns beyond conventional monitoring resolution.
✔ Lattice Compliance Report
Assessment of whether hardware operates within stable physical envelopes or exhibits instability / stress dynamics.
✔ Sovereign Receipt (SHA-256)
Cryptographically sealed integrity record suitable for audits, incident analysis, insurance, or vendor discussions.
Why This Matters
Infrastructure instability rarely announces itself as failure.
It appears first as:
• Intermittent performance variance
• Silent hardware stress
• Unexplained thermal behavior
• Efficiency losses
• Disputed incident root causes
QH8 provides physics-level visibility required for modern high-density compute and mission-critical systems.
How It Works
Step 1
Export 24–72 hour telemetry CSV from your existing systems.
Step 2
Upload via Secure Sovereign Portal.
Step 3
Receive Forensic Integrity Report within 24 hours.
Security & Data Handling
All analysis is performed using a pull-model architecture in an isolated processing environment.
• End-to-end encrypted transfer
• No persistent data retention (unless contractually required)
• Cryptographically verifiable outputs
Your production systems remain untouched.
Industry Relevance
High-Density GPU / AI Infrastructure
Detect transient-driven instability, hidden thermal stress, and variance dynamics affecting silicon longevity.
Financial & Low-Latency Systems
Establish deterministic physical audit trails for hardware integrity and anomaly attribution.
Energy-Intensive Operations
Identify inefficiency patterns, ghost cycles, and unstable load dynamics.
Infrastructure Integrity & Physics-Level Diagnostics




Data Sovereignty & Integrity Architecture
Sovereign Privacy & Zero-Liability Governance
At QH8 Technologies, sovereignty is not an add-on — it is the design principle.
We do not collect, store, or retain customer operational data.
Our role is to generate deterministic, verifiable integrity evidence while ensuring clients maintain full control of their information.
QH8 provides governance, not surveillance.
1. Total Data Sovereignty
QH8 operates under a strict Zero-Custody Model.
Customer-Owned Storage
All Forensic Receipts, integrity artifacts, and operational records are generated locally and written directly to your designated environment — private cloud vaults, on-premise systems, or air-gapped storage.Zero-Access Policy
Once generated, data remains under the client’s exclusive control. QH8 maintains no persistent access, no secondary copies, and no retained datasets.Zero-Retention Architecture
We do not function as a data repository. No client telemetry or infrastructure logs are stored within QH8 systems.
This eliminates centralized data exposure and significantly reduces information liability risk.
2. Deterministic Integrity & Third-Party Notarization
To ensure evidence remains tamper-evident, independently verifiable, and audit-defensible, QH8 applies deterministic cryptographic sealing.
SHA-256 Integrity Fingerprint
For each Forensic Receipt, QH8 computes a one-way SHA-256 hash.
The hash contains no operational data
It functions solely as a unique mathematical fingerprint
Any modification to the file invalidates the fingerprint
Independent Blockchain Anchoring
Only the cryptographic fingerprint — never the underlying data — is submitted to an independent notarization layer.
Using trusted third-party timestamping services (such as OriginStamp or Guardtime KSI), the hash is anchored to a public immutable ledger.
Public Verification
Authenticity can be validated by any external party:
Compute SHA-256 hash of the receipt
Compare with public notarization record
Match confirms integrity and non-alteration
No access to QH8 infrastructure or client data is required.


Copyright © 2026 QH8 Technologies
Contact us at contact@qh8technologies.com
📜 Underwriter Fact Sheet (PDF)
🛡️ v008-OBSIDIAN Sovereign Spec Sheet. (PDF)
